Introduction to Cyber Security
Self-paced course
Certification program
Price
Rating
Overview
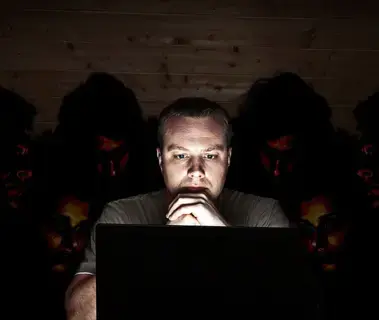
Explore the world of cyber security and develop the skills to stay safe
Modern life depends on online services, so having a better understanding of cyber security threats is vital.
On this eight-week course from The Open University and guided by Cory Doctorow, you’ll learn how to recognise online security threats that could harm you and explore the steps you can take to minimise your risk.
This course is supported by the UK Government’s National Cyber Security Programme, is NCSC Certified Training, and is IISP accredited.
Explore how to improve your network security and protect your data as it moves around the internet
Internet routers are designed to move data to its destination, which could take your data through several routers across the world. This creates vulnerabilities that allow that data to be copied.
On this course, you’ll discover tips and strategies to protect your data on a network, including firewalls and VPNs. You’ll also explore intrusion detection systems (IDS) and honeypots to detect attacks.
Assess the current threat landscape and how to protect against it
Our lives increasingly depend on digital services, which makes the internet an attractive target for criminals.
You’ll start this course by looking at the array of current threats to our information assets. You’ll assess the different vulnerable points at risk of a security breach, how threats exploit those vulnerabilities, and some countermeasures that you can use to guard against these threats.
Discover the uses of cryptography and network encryption
Cryptography is a specialised area of mathematics concerned with protecting information so that it can be transmitted and received securely.
This course will guide you through this technique for protecting information, from explaining encryption keys to exploring real-world uses of cryptography.
You will learn
1
Explain basic cyber security terminology; have skills for keeping up to date on cyber security issues; and be able to identify information assets.
2
Describe basic authentication mechanisms; have skills to improve their password security; and be aware of alternative authentication methods.
3
Identify main malware types; awareness of different malware propagation methods; and skills for preventing malware infections.
4
Describe cryptography terminology; be able to use cryptography for email; be aware of applications of cryptography.
5
Demonstrate understanding of firewalls, virtual private networks and network intrusion detection and prevention technologies.
6
Describe legal and regulatory issues relating to cyber security; and understand how to recover from security failures.
7
Apply basic risk analysis and management techniques.
Learning outcomes
Post this credential on your LinkedIn profile, resume, or CV, and don’t forget to celebrate your achievement by sharing it across your social networks or mentioning it during your performance review
Similar courses
Featured articles
330820 students
56 Days
Free trial
Subscription
English
Beginner
Video format